Life these days has become more comfortable. That is because of different digital devices as well as the strong internet supporting them.
But there is a bad side to everything great. This as well applies to the world of digital. In other words, the internet brought with it is a positive transformation in people’s lives.
Though it also came with a great challenge to keep your data safe. The Internet has given rise to cyber-attacks or cybercrimes.
Click here – The Most Chill Cities in America
What a Cyber Attack Is
It refers to a set of actions that threat actors perform. It happens a threat actor tries to gain access to unauthorized data, steal it, or cause damage to it.
A threat actor can launch a cyber-attack from any location. The attack can as well be carried out by a group using one or several TTP (tactics, techniques, and procedures).
The people launching cyber-attacks can also be called hackers, bad actors, or cyber criminals. They normally try to identify all possible vulnerabilities. These can be weaknesses or problems in a computer system, and further use them to achieve their goals.
Cybercriminals may have different motivations when launching a cyber-attack. Some of them perform attacks for financial or personal gain. But others are simply hacktivists posing to be in a political or social cause.
How It Happens
Most cybercriminals are opportunistic, with some spotting possible vulnerabilities in computer defense systems. This might involve looking for flaws in a website’s codes that enable them to insert their own codes and bypass authentication or security procedures.
While terminologies, like cyber-attacks, can conjure images of a sophisticated team with high-tech systems, the reality is usually different.
Cyber-attacks are more likely to happen through mundane mistakes, such as not changing default passwords or choosing easy-to-guess passwords on a router.
Click here – Top Benefits Of Investing In Automated Candidate Screening
Why It Happens
Every business, irrespective of size, is at risk of being attacked by cybercriminals. This is because all businesses have assets, including financial, which criminals can seek to exploit.
By using a cyber risk monitoring solution and recognizing common motives behind these attacks, you will be able to understand the risk you will face. Not to mention, you will know how to confront them better.
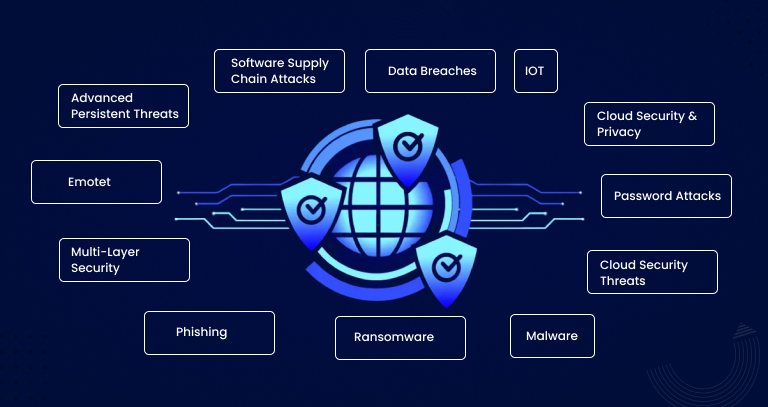
Types of Cyber Threats or Attacks
Cyber-attacks basically come in different forms via computer systems and networks. Some of the common types of cyber-attacks include the following:
-
Malware
Malicious software or malware often disguises itself as trusted programs or email attachments to exploit a virus and allow cybercriminals into your computer system.
This kind of cyber-attack usually disrupts the whole IT network. Good examples of malware include the following:
- Adware
- Viruses
- Worms
- Spyware
- Trojans
-
Phishing
This is the trick of sending fraudulent communication which comes from reliable sources. Normally, it is through emails.
This trick aims to get or steal sensitive information, such as login details and credit cards. Attackers can also install malware on your machines.
-
Ransomware
It holds files or computers hostage, by encrypting data and withholding access to details from legitimate users.
When this happens, ransom payments are usually demanded so as to restore affected systems or files.
-
SQL Injection
This kind of attack is often made through an SQL-based ill-intended code. It is normally introduced to a vulnerable application or system.
And upon a successful introduction, an SQL injection collects query results, gives a new command to the system, and carries out a prohibited action.
-
DoS and DDoS
A DoS attack often overwhelms systems’ resources, so they don’t respond to requests. In contrast, DDoS attacks are attacks on the systems’ resources. Though they usually stem from a couple of other host systems, which have been infected by a malicious software program that an attacker controls.
Unlike attacks designed to allow attacks to increase or gain access, DoS doesn’t have direct benefits for cybercriminals. For some cybercriminals, it will be enough to have the satisfaction of service denial.
But if attacked resources belong to business competitors, the benefit of attacks can be real. Another reason for DoS attacks could be to take systems offline so as to launch a different type of attack. Different kinds of DDoS and DoS attacks may include the following:
- Botnets
- Ping-of-death attacks
- Smurf attacks
- Teardrop attacks
- TCP SYN flood attacks
What Cybercriminals Target
Cybercriminals normally target resources. It could be logical or physical as long as it has one or several vulnerabilities to exploit. After the attack, resources’ availability, confidentiality, or integrity get compromised.
In some attacks, data exposure, control over resources, or damage can go beyond the ones identified as vulnerable. This may include gaining access to a business organization’s social media, Wi-Fi network, operating systems, and sensitive information, such as bank account or credit card number.
How Often Cyber-Attacks Happen
Cybercrimes now happen frequently, causing a lot of damage to businesses and people. According to a recent survey, in the first eight months of 2022 alone, more than 3.8 billion records got exposed due to cyber-attacks. This represents a 65% increase in reported data breaches and another 56% rise in all exposed records.
Solutions
Now more than before, businesses and people should proactively maintain their cyber-security. This is because the costs of cyber-attacks run well into millions, which is a price only a few are willing or able to pay.
Among the common ways, most cybercriminals get access to business data is through workers. They forward fraudulent emails, posing as someone within your business organization. Such emails aim to ask for personal information or gain access to some files.
Links in those emails look legitimate, especially to untrained workers. And it could be simple to fall prey. This explains why employee awareness is important.
The best way to protect your business against cyber-attacks and other kinds of data breaches related to attacks is to train workers. The training should involve cyber-attack prevention and teaching workers about the current online attacks. Other solutions to avoid these attacks may include:
- Check how strong your password is
- Use a VPN
- Consider using secure Wi-Fi
Closing Remarks!
These are scary times for individuals and businesses that are worried about cyber-attacks. Certainly, threats exist and are increasingly getting frequent and potent. This is why it is important to have a solid solution to counter those attacks.